Security
How to avoid getting hacked on the web
Security is one of those things people eventually learn once they’ve been hacked or had their personal information stolen. Here’s some of the the best ways to avoid getting hacked.

Just a heads up, if you buy something through our links, we may get a small share of the sale. It’s one of the ways we keep the lights on here. Click here for more.
Security is one of those things people eventually learn once they’ve been hacked or had their personal information stolen. Here’s some of the best ways to avoid getting hacked.
The year 2016 has been highly eventful in the field of digital security, with three-quarters of the year through, we’re still encountering large scale breaches and revelations of sensitive data that go back several years in the past.
Some of the most recent, and most notable, breaches in the recent couple of weeks include the availability of Dropbox’s users database on the dark market, a large dataset of more than 68 million users which dates back to the Dropbox breach in 2012.
Another recently announced breach came from Last.fm, and although the hack happened back in 2012 as well, more than 43 million users have been affected, and it’s known that Last.fm’s security at the time was very shallow, leaving the passwords in the database encrypted using only a traditional MD5 approach.
If you want to explore some of the other breaches that have happened this year, many of which have been major, you can head over to LeakedSource and take a closer look at what the state of security online is looking like.
Clearly the message here is to be thoroughly mindful of the passwords that you use for any single website, and have a collection of strong passwords spread out throughout all of the services that you’re using. This can become a tedious process if done manually, which is why we will be looking at a world-class password management platform for dispersing all your password-related security concerns, and later explore the necessary precautions to take note of; when dealing with sensitive information on the web.
Master passwords are the way to go
Passwords might sound like a preliminary security precaution, but it has shown many times in the past that even the most bright minds in the industry are able to slip up and use the same password for two different websites, and while the damage isn’t permanent, it can be bad for brand image to see how incompetent people can be when they’re in charge of millions of other people’s passwords themselves.
Creating a unique password for each website that you’re a member of and saving it into a text file on your computer isn’t the most conventional method for a good security practice, needless to say it can turn into a big mess when you’re juggling between dozens of website memberships, and you have to keep the passwords frequently updated.
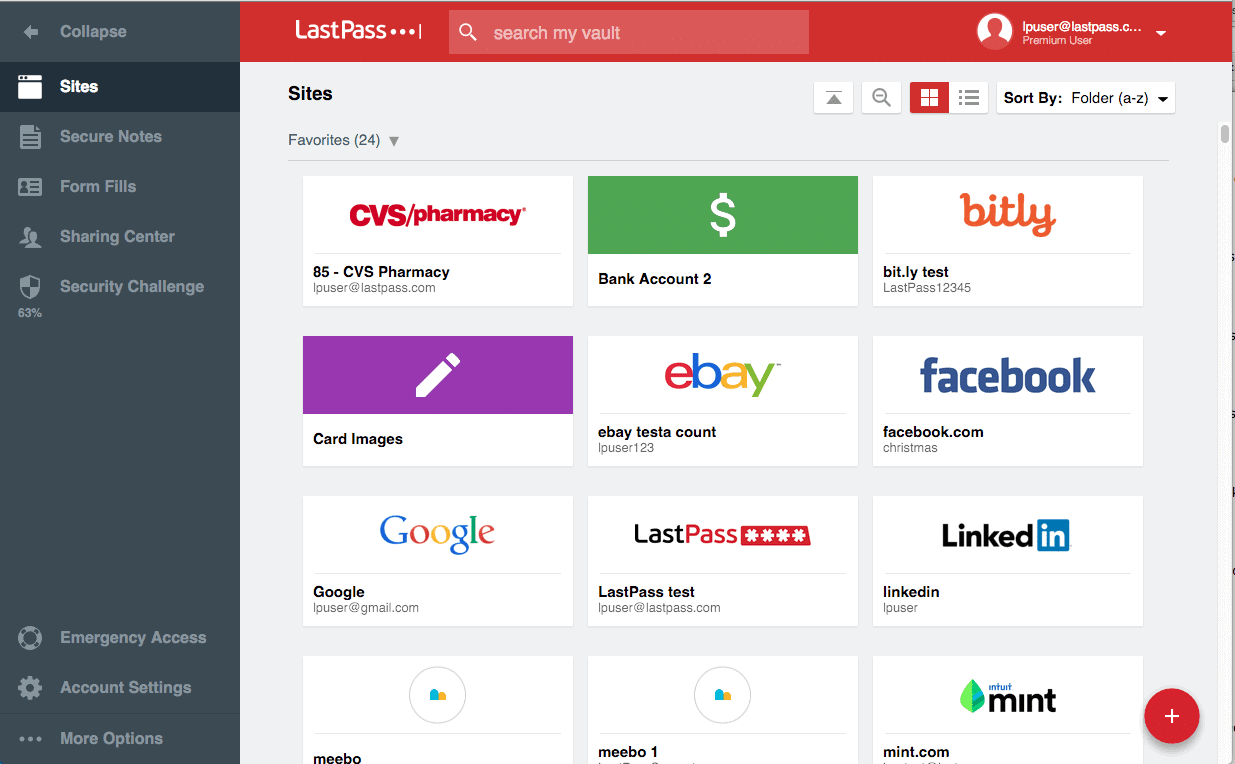
A password manager such as LastPass helps to ease the process of keeping track of all your individual passwords, while giving you a single ‘master’ password through which you can access all of your other passwords, otherwise it is safely encrypted and out of reach by hackers or those who are wishing ill upon you.
Here are some highlights of LastPass:
- Password vault — all passwords kept in a single and thoroughly secure environment, can be accessed to modify, organize and search through existing contents.
- Forms autofill — forget being worried about someone keylogging your keystrokes, LastPass automatically fills out the username and password forms for the websites that you’ve added to the password manager.
- Erratic passwords — one click password generation, as well as frequent password changing to reflect the requirements of modern security precautions.
- Online shopping — password managers like LastPass will go out of the way to help you manage more than just your passwords, but also your most sensitive information such as credit card and bank details, all in a world-class security environment.
Leaving sensitive data out of email
Maybe you’re sitting comfortably at home, or peeled to your desktop screen at work, there’s a likely chance that from time to time you’re going to receive an email that just seems too good to be true, or at least sparks a sense of sensitivity in you. It’s not unusual for hackers to craft appealing and “convincing” emails that pretend to be someone they’re not, often related to banking facilities or payment gateways. Often these emails are accompanied by fake links that are designed to steal your data in the event of you clicking on the link, and inputting any sensitive data within that opened page.
If several years ago you were told to carefully check the URL of the website that you’re visiting through email, then perhaps today the best advice is to avoid clicking any sensitive links in the email altogether. Amongst the many reasons, the most important one is that hackers can easily hijack your browser data even if you think their intention is to steal your login credentials for your bank account.
Instead, if such an email does arrive, do the right thing and visit your bank website directly and only then enter any sensitive data into the online banking system, and a far more secure approach would be to contact the bank directly and find out whether there’s any real concern to be had.
Security precautions for mobile devices

When we think of the internet or the web, we must remember that both of these terms have become heavily intertwined with the regular use of mobile devices. Ten years ago you had to go to an internet cafe in order to browse for the latest news, now all of the world’s information is available within a few taps on your smartphone device.
This creates a layer of security risks as cybercriminals understand that people are using their mobile devices not only for browsing Facebook, but also for concluding shopping and doing banking related activities. This opens smartphones up to a number of high-risk vulnerabilities that can often be overlooked as we focus on the process of getting to information fast, rather than understanding how this information is retrieved.
Mobile apps in particular are a great target for cybercriminals who wish to gain access over your mobile device, and the best way to tackle this problem is to always be aware of the application permissions that you’re giving to each of the individual apps on your smartphone. This process is usually triggered whenever a new application is being installed.
Andra Zaharia from Heimdal Security put together an extensive guide/tutorial on how to achieve complete transparency with mobile apps and their permissions, so that you can rest assured that your device won’t get hijacked overnight.