Internet
Planning for domain footprint expansion? Here are 3 reasons to check domain ownership history
While expanding their domain footprints, it is often helpful for all types of organizations to uncover a domain’s entire ownership history before actual purchase.

Just a heads up, if you buy something through our links, we may get a small share of the sale. It’s one of the ways we keep the lights on here. Click here for more.
Domain footprint expansion, the process of adding new domain names to an enterprise’s portfolio, is commonly done by big corporations as they launch new products and market lines. What many marketing departments do not account for, however, is that there are plenty of perfectly fit domain names from a branding standpoint but they may have a shady history.
Indeed, cyber attackers often register new domain names, typically in bulk, for use in various phishing and other attacks. Once these domains are no longer of use, often because they’ve been flagged as “malicious” on various malware databases, most get abandoned and end up available for registration once again.
That said, it may not be a good idea to leave domain footprint expansion decisions to business stakeholders alone. Getting advice from a cybersecurity expert and digging into a domain name’s history amongst all registered domains may be required. We listed down three reasons why.
-
Associations with Malicious Activities
Let’s say that your organization wants to invest heavily in a series of new creative products. Digital marketing experts advised you to obtain an established domain because it would rank high on search engine results pages (SERPs) faster.
After considering hundreds of options, you find out that the domain fancycake[.]net, which is at least eight years old, is available and decide to add it to your portfolio. After a few months of conducting aggressive marketing campaigns, you start noticing that the site is underperforming significantly compared to others in your portfolio.
Only then do you consult a cybersecurity professional who tells you that the domain has ties to spamming activity. So now you have to make a critical decision—drop the domain or clean up its act. The lesson? Your department should have checked the domain’s ownership history before purchase.
While the domain seemed perfect for your business expansion, a run through Threat Intelligence Platform (TIP) showed that fancycake[.]net is suspected of ties to spamming just as your cybersecurity consultation revealed. It may have been dropped by its previous owner, in fact, due to its inclusion in a blacklist.
-
Connections to Malicious Organizations
Attackers go to great lengths to establish legitimate-looking companies to fool their victims. One example of such an organization could be Nexperian Holding Limited, which has lost cases to several trademark owners in domain name disputes handled by the World Intellectual Property Organization (WIPO).
That said, say you’re planning to buy the domain zpv[.]tech for one of your business expansion requirements. Apart from checking if the domain is available for registration, it would also be best to perform a domain name history lookup on it to avoid similar repercussions, as in the previous example.
We subjected zpv[.]tech to a domain ownership history search and found that it has connections to Nexperian Holding Limited.
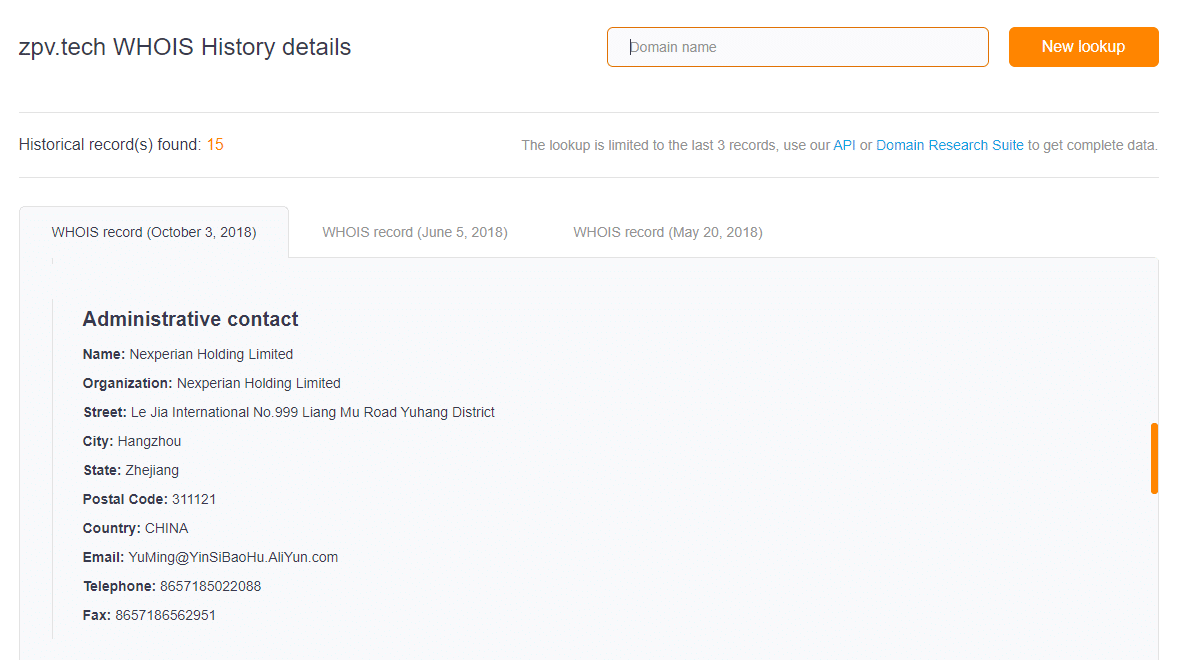
Apart from the trademark infringement cases the company was involved in, you should also know that Nexperian Holding Limited has been cited for selling counterfeit goods. That said, the domain may have been or remains listed in blacklists or under investigation by law enforcement agents.
-
Ties to Identified Criminals
Another domain purchasing no-no is buying one that belonged to a known cybercriminal. Any associations with malicious activity could cause reputational damage to your entire organization. Buying a domain previously owned by a cybercriminal, especially one on a list such as Cyber’s Most Wanted of the Federal Bureau of Investigation (FBI), is thus a terrible idea.
So, let’s say that you want to acquire the domain tianjincentre[.]com. It’s an established domain, and its registration will expire in June 2020. But a thorough check of its domain name history revealed that between 13 December 2013 and 13 December 2014, its registrant was an individual named “zhang shi long” from Tianjin.
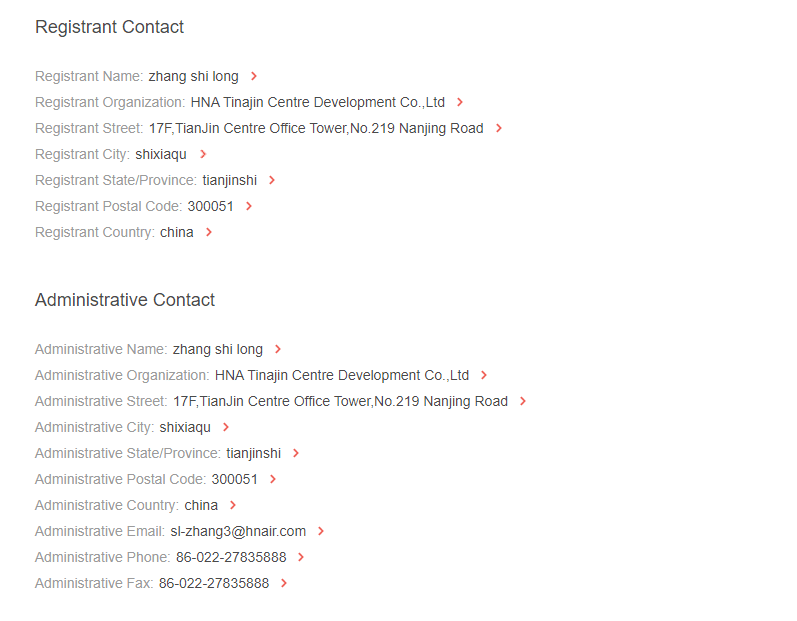
A web search for the name would let you know that a certain Zhang Shilong is wanted by the FBI. While you can’t be sure if the two individuals are the same, you probably should err on the side of caution.
While expanding their domain footprints, it is often helpful for all types of organizations to uncover a domain’s entire ownership history before actual purchase. Solutions like WHOIS History Lookup can help domain buyers make sure that their choices do not have a past that can put their businesses in hot water.
Editor’s Note: Jonathan Zhang is the founder and CEO of WhoisXML API—a domain and IP data intelligence provider that empowers all types of cybersecurity enterprises to build better products and achieve greater network security with the most comprehensive domain, IP, DNS, and cyber threat intelligence feeds. WhoisXML API also offers a variety of APIs, tools, and capabilities, including Threat Intelligence Platform (TIP) and Domain Research Suite (DRS).