Business
What is compliance & record management
Use automated tools helps you to organize all your data (both physical and digital neatly).
Just a heads up, if you buy something through our links, we may get a small share of the sale. It’s one of the ways we keep the lights on here. Click here for more.
An internal auditor’s request for information on records management and documentation translates into fear and uncertainties for many departmental heads.
You should not only achieve the retention over many years but also ensure that the information is adequately protected.
Definition of Records Management
Records management entails documenting information and protecting it over the required period. With the technological advancements, it has become possible for businesses to obtain data for people with whom they may never transact! This may come in the form of job applications and marketing aides. You’re required to have a proper mechanism to collect, sort, store, and dispose these documents at the appropriate time.
Some regulatory bodies will only focus on data related to employees and customers. However, some of the regulations such as the General Data Protection Regulation (GDPR) requires that you protect all the data that you interact with from any form of breach. For example, information collected by your marketers may appear unnecessary after the lead generation program but it’s a significant data risk for your business.
Typical Retention Schedules: What are they?
Various industries have different record retention schedules. For example, it’s a requirement that all information collected by banks be stored for 5 years. The most commonly used categories of data retention programs include 3 years, 5 years, 7 years, 10 years, or permanent retention schedules.
How Data Retention Affects Your Organization
The development of technologically advanced data collection methods has complicated the data retention and protection process. Unlike the old days where you could collect documents and store them in a guarded warehouse, today’s environment is highly digital! This requires that you invest in data storage programs and institute security against data breach.
You should also ensure that you have proper tracking systems. This will help you to dispose of documents that have surpassed their retention limit easily.
5 Crucial Steps to Create a Records Management Policy
You’re required to use ISO 15489 guidelines when preparing for this policy. Also, ensure that you devise measures to ensure compliance. The steps include:
Review the Assets and Storage Locations
Ensure that you comprehend all the information that you store and the specific storage locations. This will help you to sort the data based on parameters necessary to enhance security against data breach. The records can be classified as:
- Operational. This is the information that is essential for daily business operations. Include customer data, employee information, organization charts, tax information, data access and authorization, marketing information, human resource documents, and minutes for Board of Directors meetings.
- Legal. This data revolves around the legal liabilities of a business. It includes articles of incorporation, lawsuits, third-party vendors’ information, consent forms, and insurance policy information.
- Emergency. This involves all the information required in ensuring business continuity and resolving disasters. It includes emergency access authorization, facility blueprints, policies and procedures, security codes, and technical system documentation.
- Financial. This information entails assets, liabilities, and financial history. It includes the investments details, payroll information, ledgers, and banking documents.
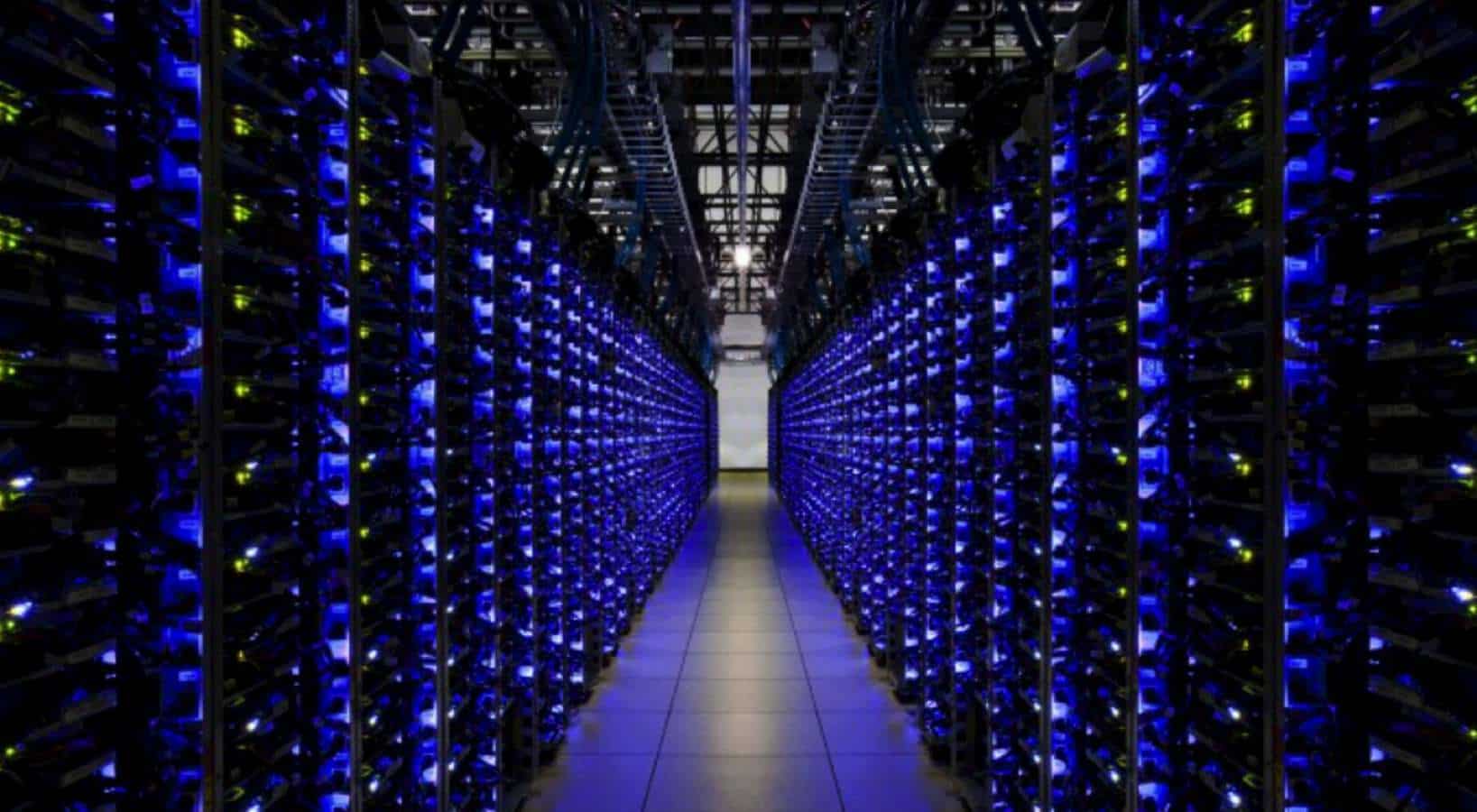
- Based on Location. The information can be stored in the networks, servers, cloud storage, onsite and offsite locations, and backups.
Review Data Importance and Rate Risk
It’s critical that all policies focus on crucial information whose interference would result in a discontinuity or financial loss. These questions are necessary during the review:
- Is the information required for business continuity?
- Will the loss of data lead to a monetary loss?
- Is it costly to reconstruct the data?
- How rapid should you recover information in case of loss?
- Can the information be obtained from other sources?
- Are the documents physical or digital?
Review the Risks to the Information
When deciding the retention period, you should consider the long terms need of the information and the cost of recovery in case of a loss. These are the guiding questions:
- Who is in charge of the data?
- Do you have adequate controls such as encryption and firewalls?
- What is the format for your information?
- Is it possible to document all transactions?
- Who can access the information?
- How do you regulate/ authenticate control?
Monitoring Records Protection
If you fail to monitor your information frequently, you’ll suffer from integrity noncompliance!
- Are you frequently monitoring all software, servers, and networks for risks?
- Are you updating your software?
- Do terminated employees continue to access data?
- Are you monitoring the external threats?
- Are you reviewing your access?
Disposal of Records
You should have a plan to dispose of your records. Ensure that you do not violate a regulatory requirement in the process. Ensure you have backups and a verified disposal agency to complete the process.
Use of Technology in Records Management
Use of automated tools helps you to organize all your data (both physical and digital neatly. It saves you on time and resources required for the audit process thus making it easier to comply with regulatory bodies.
Editor’s Note: Ken Lynch is an enterprise software startup veteran, who has always been fascinated about what drives workers to work and how to make work more engaging. Ken founded Reciprocity to pursue just that. He has propelled Reciprocity’s success with this mission-based goal of engaging employees with the governance, risk, and compliance goals of their company in order to create more socially minded corporate citizens. Ken earned his BS in Computer Science and Electrical Engineering from MIT. Learn more at ReciprocityLabs.com.
Have any thoughts on this? Let us know down below in the comments or carry the discussion over to our Twitter or Facebook.
Editors’ Recommendations:
- Network segmentation and PCI compliance
- PCI DSS log management
- Scoping a SOC2 audit
- Audit requirements – Private US companies
- Risk management plan – What it is for?




























