Internet
Stay away from fake news sites with reverse domain lookup tools
With cybersecurity research tools that allow users to do reverse domain lookups, publishers can protect their media brand from falling victim to bogus sites and copycats.

Just a heads up, if you buy something through our links, we may get a small share of the sale. It’s one of the ways we keep the lights on here. Click here for more.
The global media community is a small, tight-knit community despite its size and reach. The idea of six degrees of separation rings true in this industry—somebody knows someone from a different department or competing news outfit. That alone should make it easy to spot impostor news publishers that came out of nowhere—if only it were that simple.
But the democratization of publishing resources has enabled virtually anyone, including fake news producers, to set up sites and social media accounts to host their content. Perpetrators attempt to pass off their sites as real media publications and deceive users into believing their fake claims and cyber propaganda.
Take the case of an individual named Jestin Coler as an example. He resides in a suburb in Los Angeles and has been found guilty of proliferating fake news on several sites that he maintains.
In this post, we’ll discuss how readers and media companies can identify and stay away from junk news producers with reverse domain lookup tools such as Reverse WHOIS API and Reverse WHOIS Search. But first, let’s delve into how malicious actors proliferate bogus news sites.
How Are Fake News Sites Created?
It starts with a legitimate-sounding domain name. Cybercriminals usually register domain names that closely resemble those of mainstream news organizations. They also include local keywords in their domain names, as commonly practiced by traditional newspapers.
In Coler’s case, these domains include NationalReport[.]net, USAToday[.]com[.]co, and WashingtonPost[.]com[.]co. While no legitimate news publication goes by the name “National Report,” USA Today is a legitimate news publication founded by Al Neuharth on September 15, 1982 in Virginia. It’s owned by the Gannett Company. Washington Post, on the other hand, is a major U.S. newspaper published in Washington and founded way back in 1877. The newspaper, owned by Nash Holdings, has even won 47 Pulitzer Prizes throughout its life cycle.
After being found out as early as 2016, you probably would have thought he’d stop fabricating bogus news but he hasn’t. National Report still lives on. It claims to be “America’s #1 independent news source.”

Prove Whether a Site Is Hosting Fake News with Reverse Domain Lookups
How can we tell if a site promotes false reports? Looking under the hood helps. Several publications have already proven that Coler is a fake-news peddler. He’s even cited in Wikipedia’s list of known fake news publishers.
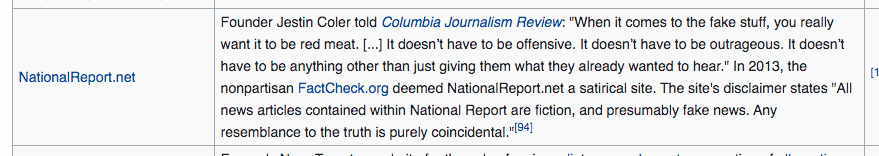
Based on that list alone, we can see that Coler ran several other fake news mills, which include Conservative Frontline, Denver Guardian, DrudgeReport[.]com[.]co, and United Media Publishing. The list tells readers to stay away from the sites to avoid misinformation. Some of the sites there no longer exist since their discovery. But what if Coler put up other sites that have yet to be discovered? We put that theory to the test.
We used Reverse WHOIS Search to look for more domains that Coler most likely owns using “Jestin Coler” as a search term. The tool allows users to input a company name, phone number, email address, or any other search term that can be found on a WHOIS record. We used the Advanced search and ticked Historic as Coler may have started using privacy protection when registering new domains. Looking for historic WHOIS records will, therefore, provide us with better results.
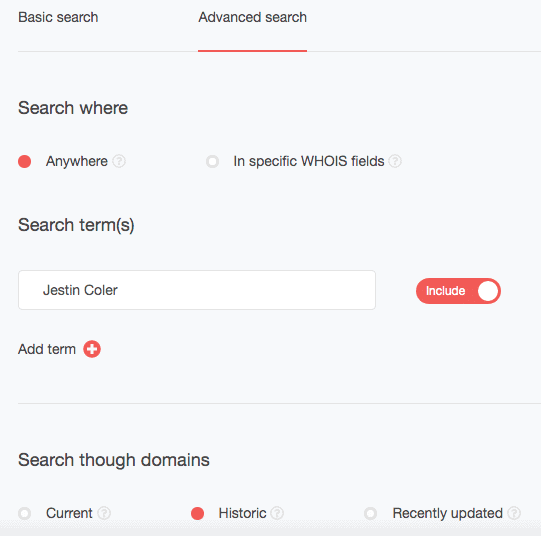
We found four domains with the search term in their WHOIS records.
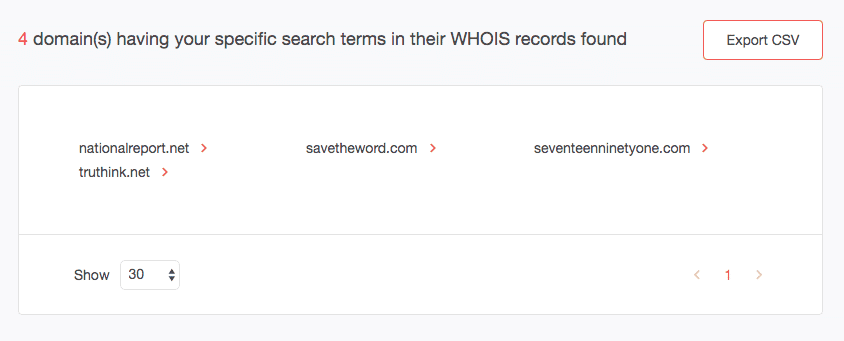
We already know he owns NationalReport[.]net. So we just built historic WHOIS records for the three others by clicking the red arrow beside each name and choosing “Build a historic WHOIS report.”
We found that Coler owned truthink[.]net until March 24, 2017. The current owner’s name has since been redacted in the WHOIS record. Coler may still be the owner or has passed it on to someone else. The name of savetheworld[.]com’s current registrant has also been stripped from the WHOIS record but Coler owned it until April 12, 2017. Finally, seventeenninetyone[.]com’s historic WHOIS report revealed that Coler owned it until December 3, 2017.
From several of the WHOIS reports we built, we also found that Coler used the same email address when registering domains, that is, jestin@savetheworld[.]com. Users can perform a reverse WHOIS search by email address as well to retrieve associated domains. In some cases, they can get the email address from the site’s contact or social media page.
You can use this data to support Uniform Domain-Name Dispute-Resolution Policy (UDRP) and trademark disputes. That is true for sites like USAToday[.]com[.]co and WashingtonPost[.]com[.]co. Clearly, their rights were being trampled by the look-alike domains.
Of course, the use cases for Reverse WHOIS Search, and its API version, Reverse WHOIS API, aren’t limited to uncovering infringers and fake news creators. The tools are also useful for obtaining the hostnames and domains used by known cybercriminal gangs. They can also support third-party risk assessment by providing users with all official domains owned by potential partners.
With cybersecurity research tools that allow users to do reverse domain lookups, publishers can protect their media brand from falling victim to bogus sites and copycats. That way, they can ensure that only the absolute truth reaches their loyal readers. Reverse WHOIS API and Reverse WHOIS Search are two valuable tools that could help with this goal.
Editor’s Note: Jonathan Zhang is the founder and CEO of Threat Intelligence Platform (TIP)—a data, tool, and API provider that specializes in automated threat detection, security analysis, and threat intelligence solutions for Fortune 1000 and cybersecurity companies. TIP is part of the WhoisXML API family, a trusted intelligence vendor by over 50,000 clients.