Mobile
How to protect yourself and your smartphone at a protest
Your phone can be used against you in multiple ways, here’s what to know.

Just a heads up, if you buy something through our links, we may get a small share of the sale. It’s one of the ways we keep the lights on here. Click here for more.
If you plan to exercise your First Amendment rights to peaceful assembly to protest the injustices in the system, there are a few things you should consider so you are as safe as possible.
Things like knowing where you are going, for a start. Also, how to get away if needed, and what clothes to wear, are all essential.
What’s also essential is to think about how to secure your smartphone, not just from loss or theft but also from surveillance.
You also need to plan for disrupted communications. Cell tower jamming is a favorite. That many devices in one place also slows down the network.
I mean, have you ever been to a sporting event or conference where the WiFi was crawling? The same thing applies to protests.
Assume the protest is being watched

Work on the assumption you will be tracked. That could be in real-time, or it could be after the fact. It could take many forms, including photos, video, and facial recognition. Credit card receipts, transit passes, etc, are all tracked.
The authorities will use facial recognition. Real-time might take too many resources. Assume images and video posted to social media will be scanned. Consider this if you do decide to post any images while you are there.
It might be wise to stick emoji stickers over faces or blur them out completely before you post. It’s not just your safety at risk.
Surveillance is often done from aircraft. Same with drones. Some precincts have more exotic surveillance like X-Ray vans.
Your wireless communications are also watched
Your smartphone is a treasure trove of data for anyone looking to identify you or bring charges against you.
Stingrays can trick your phone into connecting to them instead of the local cell towers. That lets the authorities siphon off information (such as SMS messaging, identifying information, and more) without you knowing.
Your wireless provider will also be asked for information on your movements. All it takes is a request from the police or other authorities.
Any intelligence gathered about protestors would then be used to create relationship charts and other information for future monitoring efforts.
WiFi can be tracked just as easily as a Stingray tracks your cell service. If you connect to an Open Network, the data you send across it isn’t encrypted, leading to an easy interception.
The authorities aren’t the only ones you need to worry about here. Criminals also use this tactic to target crowds to siphon off bank details and other information that can be used to steal your identity or cash.
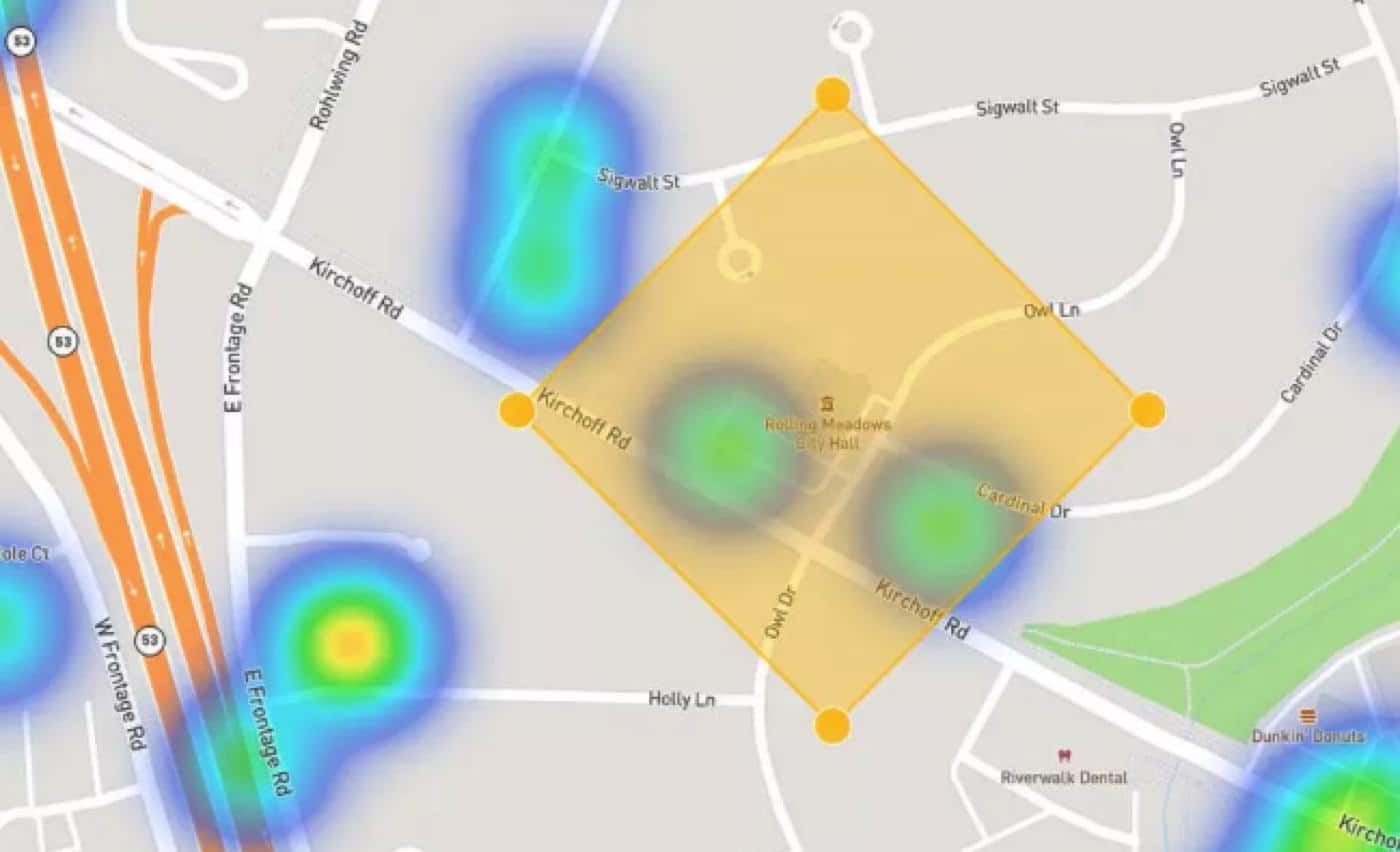
The other thing on your phones? GPS location data. The New York Times showed that this data can be bought by pretty much anyone and reconstructed to show your movements. Yikes.
Or this one from The Guardian, which outlines how “anonymized location data from opt-in cellphone apps” was used to show the movements of protestors from lockdown protests. The upshot of all of this? Assume your phone is being tracked.
How to minimize your risk while protesting

So, you’re now aware that you and your mobile device will likely be tracked while you’re out at a protest. Knowing that risk is better than going out unprepared.
Assume that you also might be detained by law enforcement, and any mobile devices you carry are confiscated, searched, and possibly stolen.
Whatever happens, once it’s out of your hands, your phone data is no longer yours and you must assume that it has been downloaded for future analysis.
That’s not to say you shouldn’t take a phone. Aside from their utility as a communication device, most phones nowadays have a capable camera attached to them. That might enable you to have exculpatory evidence if you get charged.
Here are more tips on how to protect your smartphone at a protest:
- Turn off biometrics: seriously, your Fifth Amendment rights don’t apply to biometric locks. Make sure they’re off and make sure you have a long PIN or password set instead
- Enable disk encryption: Most Android or iOS devices do this automatically if you enable a passcode, but double-check
- Remove any unnecessary apps: Treat your phone like a burner and uninstall everything but essential apps.
- Log out of any apps: Seriously, anyone can use your accounts if you leave them logged in. If you need access, try to set PIN codes for individual apps if possible
- Back up your phone: Back things up before you go. Also, make sure that the backup is encrypted and protected by a password, and two-factor authentication
- Use encrypted communications wherever possible: Use messaging apps that support encrypted messaging, such as WhatsApp or Signal, set messages to expire automatically if possible, and if you need to send unencrypted messages, use prearranged codes instead
- Shut off WiFi: Just do it. You’re not likely to be in reach of a WiFi hotspot while inside a big crowd anyway. Any hotspots you might see are probably honeypots created by police officers or criminals
- Disable location services: You don’t need this on unless you’re trying to use your Maps app, and you should really have a physical map
- Disable Bluetooth: Yes, you won’t be able to use your AirPods, but nobody will be able to track you with Bluetooth either
- Turn off your data plan: If you don’t need it to be on, turn this off as well. It might hamper your ability to use encrypted communication apps, but you can always turn it on briefly to check for messages, then turn it off again
Finally, Turn your phone off completely: The best defense against wireless tracking is to completely turn your phone off unless you’re using it at that moment. This also makes it harder for anyone to access the data if you’re separated from your handset.
Use a burner phone at protests

If you don’t already know why it’s wise to use a burner phone and keep your main phone at home, here’s a little refresher, illustrated by the below tweet from Unicorn Riot. There’s a little bit of tech called the Stingray that the police like to use to collect cell phone data in an area.
When they mount them onto drones, it’s then airborne and can potentially siphon up data from a huge area. Your cell phone data. That of the person next to you. That of the cell phones the authorities are carrying.
Everyone will get their cell phone data in the hands of the police. You don’t want that. Your details are tied to your account, and to your home address.
The advice in the reply is also good. Use a VPN app to encrypt your data connection. Use a five-digit PIN, if your phone supports it, and turn off all biometrics (yes that means fingerprint unlock, Face ID, or Touch ID).
Heck, it takes seconds to make a new Google account, and if you’re using a burner phone, you don’t want to sign in with your main account.
This phone should be using a SIM card that you paid cash for. That way, it’s not linked to your name. Even better, buy several, and use one SIM card per time you protest.
You don’t want to be trackable back to your home and having that burner SIM on when you get to your front door makes all the efforts you’ve just gone to worthless.
On this phone, you should have as little information as possible. Only have the apps you absolutely need for communication. Don’t connect it to any of your cloud services.
Only have the numbers in Contacts that are essential. Consider putting fake names here. If you need to log in to any app to use it, see if you can set a secondary PIN code to access it.
Lastly, set up new accounts for all the apps you use on this phone, and never log in to anything you use on your normal phone with your main credentials.
Temporarily disable Face ID on your iPhone during protests

You should be using biometric locks on your iPhone. It’s more secure in most situations than a short pin code, and easier to use.
That said, you don’t want biometrics on during a protest, as legal precedents say that the authorities can force you to unlock your devices.
There is a way to have both biometrics on and be able to disable them quickly. It involves using the iPhone’s built-in Emergency Calling feature.
You can access this by either tapping the side button five times or by holding the power and either of the volume buttons for about two seconds.
The press-and-hold method is probably easier, as it works on any iPhone and doesn’t require you to set up the five-press method.
This opens the emergency SOS screen, which has a slider to call for help, or a button to show your medical details. You don’t need to do anything from this screen.
All you wanted was to get to that screen, which temporarily disables Face ID or Touch ID. Now anyone wanting to get into your iPhone needs the passcode, which you aren’t required to give out.
Oh, and never hand your phone to anyone. We mean anyone. If the authorities actually need your phone, they’ll just take it. They won’t ask. So don’t hand it over if they do ask.
Print out any necessary information
We don’t mean to print out your contacts list, but there are a few things you should probably print just in case. That includes maps of the area you’re protesting in, or even better, buy a physical map of the area.
Have prearranged areas to meet up with the people you went to the protest with. It’s also worth working out some pre-arranged signals, so you don’t have to type out long instructions.
Turn your smartphone off when not being used. You can turn it on every so often to check messages or calls but keeping it off minimizes tracking while also protecting your battery life.
Always have a plan
The biggest thing to take away from all of these, frankly scary, preparations? Being prepared and having a plan, then doing your best to stick to that plan, is the best way to avoid trouble.
Think back to your childhood. Scouts told you to “Be Prepared,” and GI Joe told you that “knowing is half the battle.” That advice rings true whatever you’re doing, whatever age you are, and wherever you find yourself.
What do you think? Do you have any more tips for people looking to protect themselves while protesting? Let us know down below in the comments or carry the discussion over to our Twitter or Facebook.
Editors’ Recommendations:
- PSA: Don’t loot products from the Apple Store – they’re tracking you
- Walmart employees say its anti-shoplifting AI is complete trash
- Trump signs executive order aimed at social media companies like Twitter
- A new report suggests that almost half of the tweets regarding the coronavirus are probably from bots




























