Security
What is two-factor authentication? (and why it matters)
Two-factor authentication can be implemented each time someone tries to access their account.
Just a heads up, if you buy something through our links, we may get a small share of the sale. It’s one of the ways we keep the lights on here. Click here for more.
When it comes to keeping yourself safe on the Web, few things are more important than protecting your personal information. It is estimated that one in two North American internet users suffered an account breach in 2021.
These breaches can come in many forms — be it a successful hack of a company resulting in knowledge or an individual having their login information stolen while using an unsecured network.
Because hackers can use this information to steal your personal data and access financial accounts, implementing additional security factors such as two-form authentication can protect your private information.
Two-factor authentication — what is it?
Short Answer: Two-step verification
Two-factor authentication, also known as multi-factor authentication, is a system that requires users to provide an additional form of authentication beyond their username and password to verify their identity.
This second form of authentication can come in several forms, such as a uniquely generated code that is sent to an individual’s cell phone, or even a biometric authenticator like a facial scan or fingerprint.
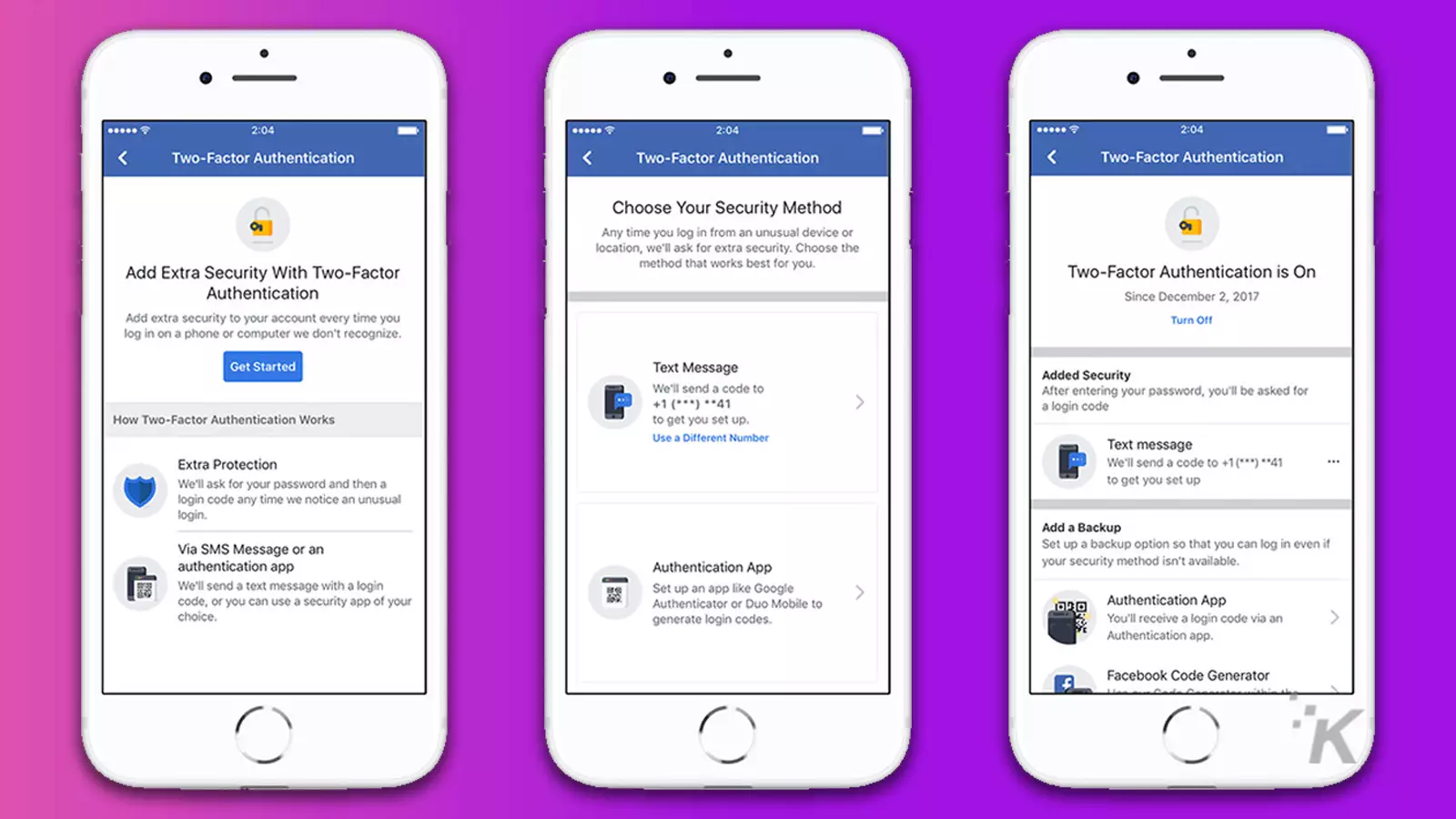
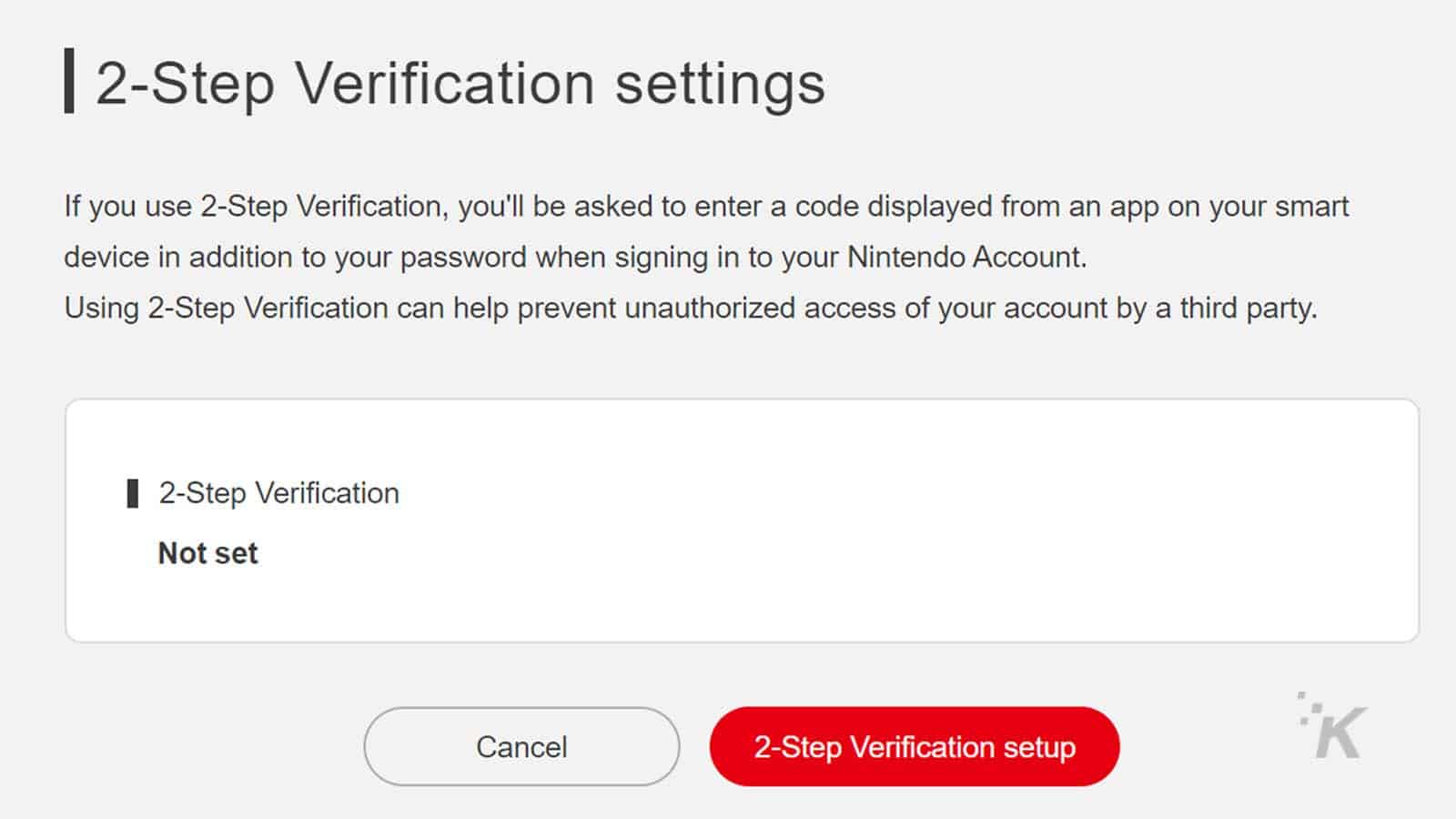
Two-factor authentication can be implemented each time someone tries to access their account. It could be selectively enforced for situations such as when accessing an account from a new device or GPS location.
Most websites require a user first to enter their username and password when logging in. After inputting this information, the website proceeds to the second step of the authentication process.

The exact form of two-factor authentication used for a particular device or account tends to vary based on the website or device being used.
While unique security questions such as “What was the model of your first car?” could help make it more difficult for a hacker to access your account, they are considered to be the same type of information as your username and password — namely, information that is known and provided by the user.
This information could also be leaked or guessed, allowing a hacker to access your account.
With two-factor authentication, the second form of authentication is generally dependent on something only the authorized user would possess or something that is inherent to the user.
Do yourself a favor and look into a free password manager
Discover the best free password managers to keep your online accounts secure. From NordPass to Bitwarden, we cover it all.
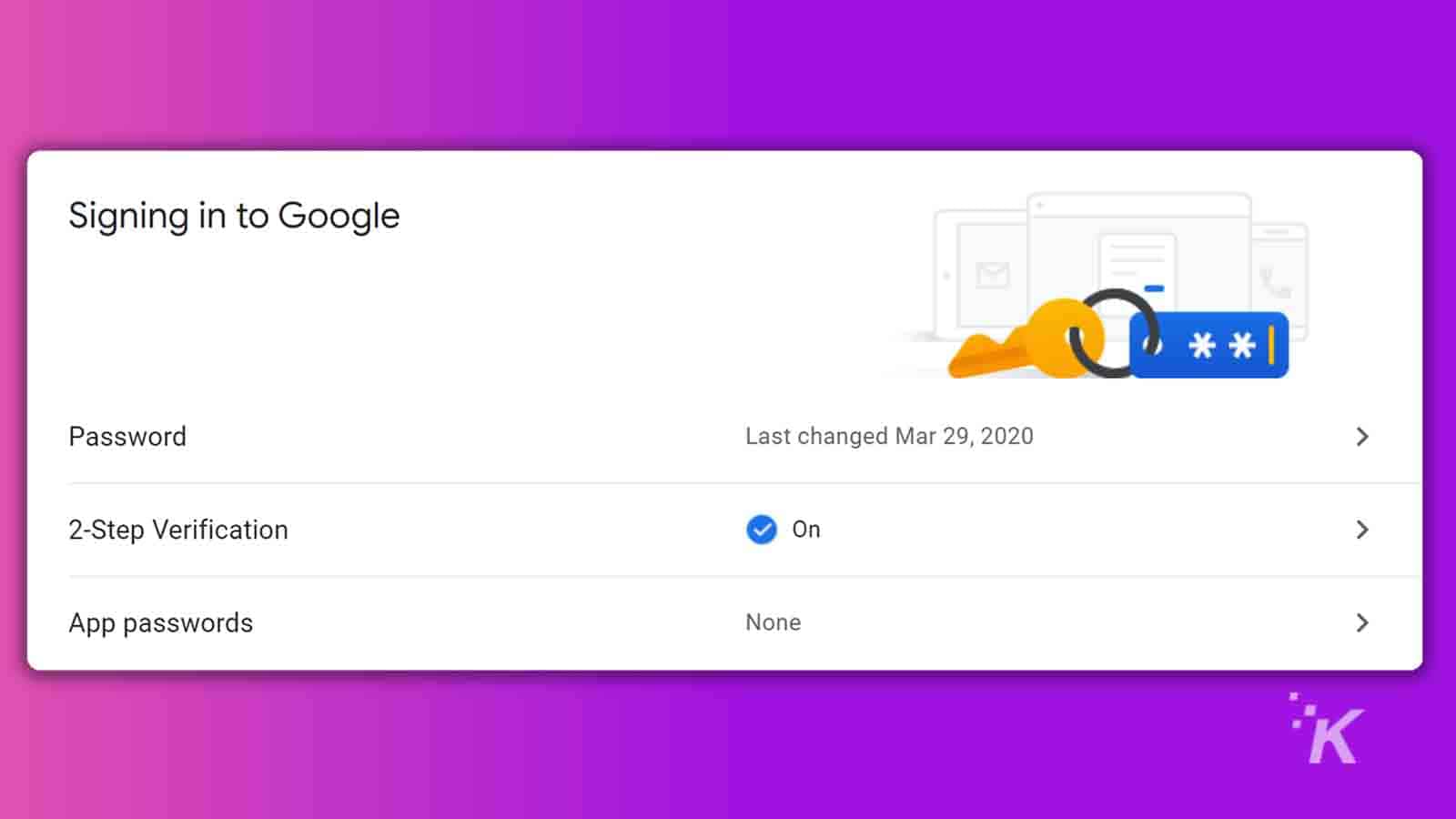
For example, Google accounts use phone-based authentication, which sends a prompt to the phone number connected to the user’s account after a login attempt is made. The user must tap the prompt on their phone to authenticate the login.
A unique numerical code for other websites will be texted to the user’s device. The user typically has limited time to enter the code before it expires.
In both cases, the user must possess the authorized phone to complete the login.
Diving into the why of two-factor authentication
To some, adding two-factor authentication to their accounts can feel like an inconvenience. But as Steven Price, founder of Tech Rockstars explains:
“Two-factor authentication can ultimately be what makes the difference between a hacker getting into your account, and keeping them out. Even if you have a strong password, companies suffer data breaches all the time. If your username and password were compromised, a hacker could use that login information to access personal information, including any financial accounts linked to that account. With two-factor authentication, on the other hand, the password is useless on its own.”
Regardless of how a hacker gains access to your password — be it through hacking, a phishing attack or guesswork, two-factor authentication can present an insurmountable barrier.
Someone else might be able to guess your password, but it’s far less likely that they’ll also be able to steal the phone that receives the one-time login code used for your authentication process.
And facial recognition technology has become increasingly advanced, differentiating between a “real” person and a photo.
The fact that two-factor authentication can keep hackers out of your accounts should be reason enough on its own to adopt it. So too should the prevalence of cyber attacks in general.
Consider these statistics: Over 550 healthcare organizations in the United States suffered a data breach in 2022.
Forty-five percent of emails sent in 2022 were unsolicited spam emails, many of which involved phishing schemes and malware. Worldwide, it is estimated that 30,000 websites are hacked every day.
Needless to say, there are countless opportunities for usernames and passwords to get stolen — particularly if you have accounts on many different websites.
You can’t control the quality of digital security used by other websites. But you can control the login process that guards your account information.
With two-factor authentication, you can keep essential data safe, no matter what.
Keeping yourself safe with two-factor authentication
It is estimated that cybercriminals will steal 33 billion records in 2023.
While you can’t always control what happens to your data online, you can take steps to protect yourself should your usernames or passwords ever become compromised.
By implementing two-factor authentication on your accounts, you can have confidence that your information will be kept safe, and that you’ll be able to keep unauthorized individuals from accessing it for malicious purposes.
Have any thoughts on this? Drop us a line below in the comments, or carry the discussion over to our Twitter or Facebook.
Editors’ Recommendations:
- How to find saved WiFi passwords on Mac
- How to turn your WiFi password into a QR code‘
- How to find saved WiFi passwords in Windows 11
- Netflix’s password-sharing saga continues