How-To
Think someone is freeloading on your WiFi? Here’s how to tell, and what to do about it
Dang WiFi leeches…

Just a heads up, if you buy something through our links, we may get a small share of the sale. It’s one of the ways we keep the lights on here. Click here for more.
WiFi is one of the greatest inventions of our time, giving wire-free connectivity to all of our gadgets. At least, until it stops working properly. If you’ve noticed a drop in your wireless connection speeds recently, someone might be tapping into your WiFi to use your internet connection free of charge.
This is a far smaller problem nowadays than it used to be, as most routers come with at least some level of security configured. If you buy a consumer router from the store however, you’ll have to set WiFi passwords manually, something you might not know to do if this is your first non-rented router.
It’s also a problem for some people using routers provided by their internet service provider (ISP), as the pre-configured WiFi security settings are usually trivial for any determined attacker to figure out.
That means that even if you think you’re protected, you still might have unwanted guests on your network. Here’s how to figure out if they are, and also how to kick them off so they stay off.
Do you have a WiFi freeloader on your network?

The first step is to see if it’s just your router needing a reboot, or if someone is actually freeloading. If there aren’t many WiFi devices in your home, turn them all off for a few minutes, then watch the WiFi activity LED on your router. If it’s flickering, it’s a good chance someone else is using your WiFi.
The thing is, this method doesn’t really work well nowadays because everything from our phones to our fridges could have WiFi connections. Remembering to turn them all off is a chore, and turning them back on again afterward doubly so. Here’s a couple of comprehensive ways to sniff out the snoops and get them off your network for good.
There’s an app for that
There’s a huge number of applications that can sniff out unauthorized network users and their devices. Cross-checking those device identifiers versus times you know you used your network or had friends over can give clues to if someone is swiping your bandwidth.
F-Secure Router Checker: F-Secure has a web-based checker as part of its free offerings, so you don’t even have to install anything on your PC. Just go to the link, and hit the big blue Check your router button. This tool looks for stealthy setting tweaks that could indicate someone is hijacking your internet.

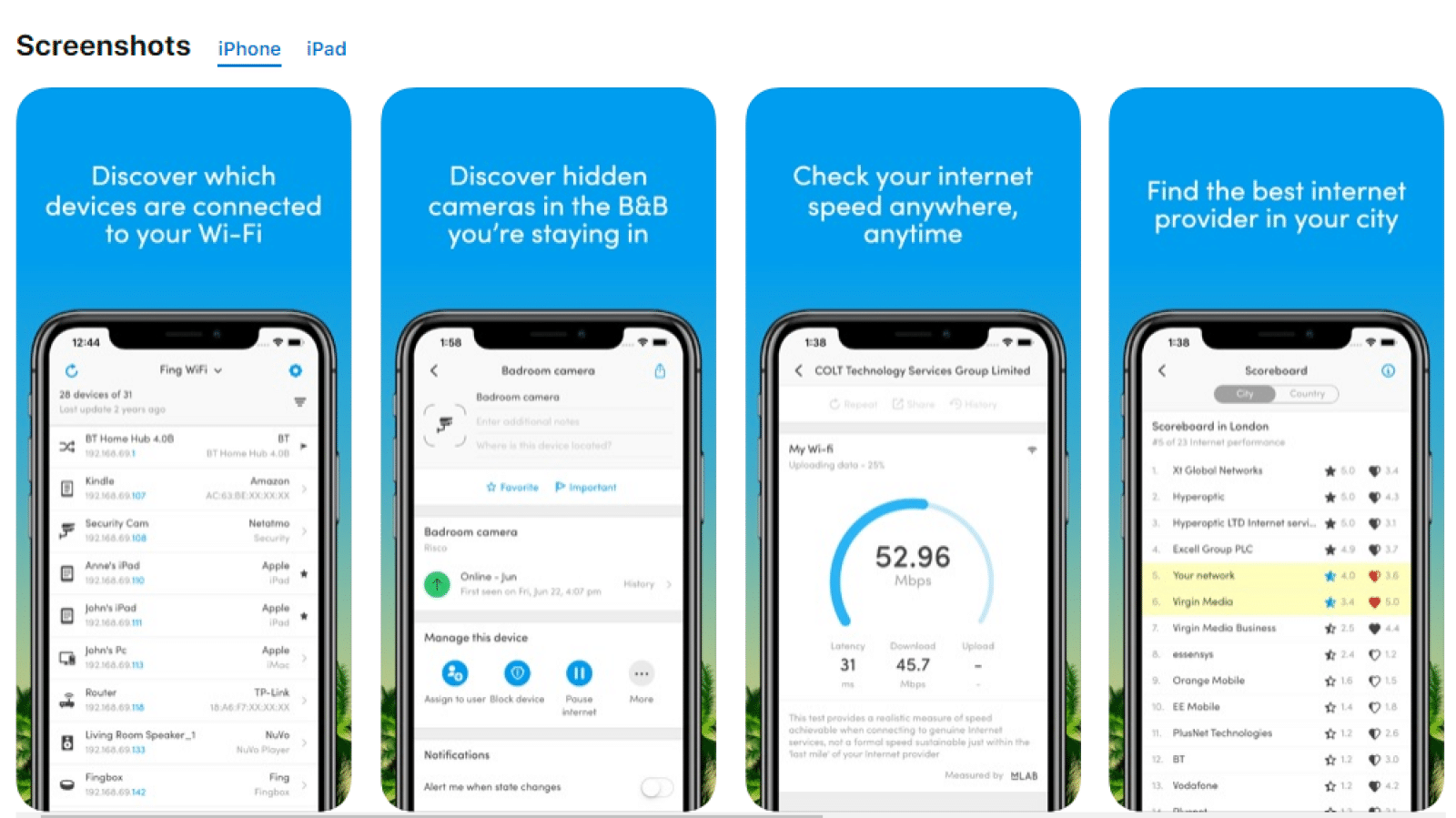
Fing: Fing is great. It’s got iOS and Android apps, for those of us who like to do everything with our mobile devices. It’ll show you the devices connected to the network you’re also connected to, details about their connection, and even their names most of the time. It’ll also sniff out any hidden cameras in the B&B you’re staying in, so it’s a nifty tool for any traveling.
Wireless Network Watcher: This app works on both Windows and Mac, and helps users look for suspicious wireless activity while monitoring all connected devices. It’s a little basic, but could be all you need to find uninvited users.
The pro way
If you’re thinking someone might be draining your WiFi bandwidth, there are always the administration logs of your router. Getting to them means logging into your router, usually, that’s accessed by typing 192.168.1.1, 192.168.2.1, or 192.168.0.1 into your browser address bar and logging in with your admin password.
Then it’s the Administration tab from the left side menu. On my Linksys Xbox router, it’s a button saying Download log to get the log file to read.
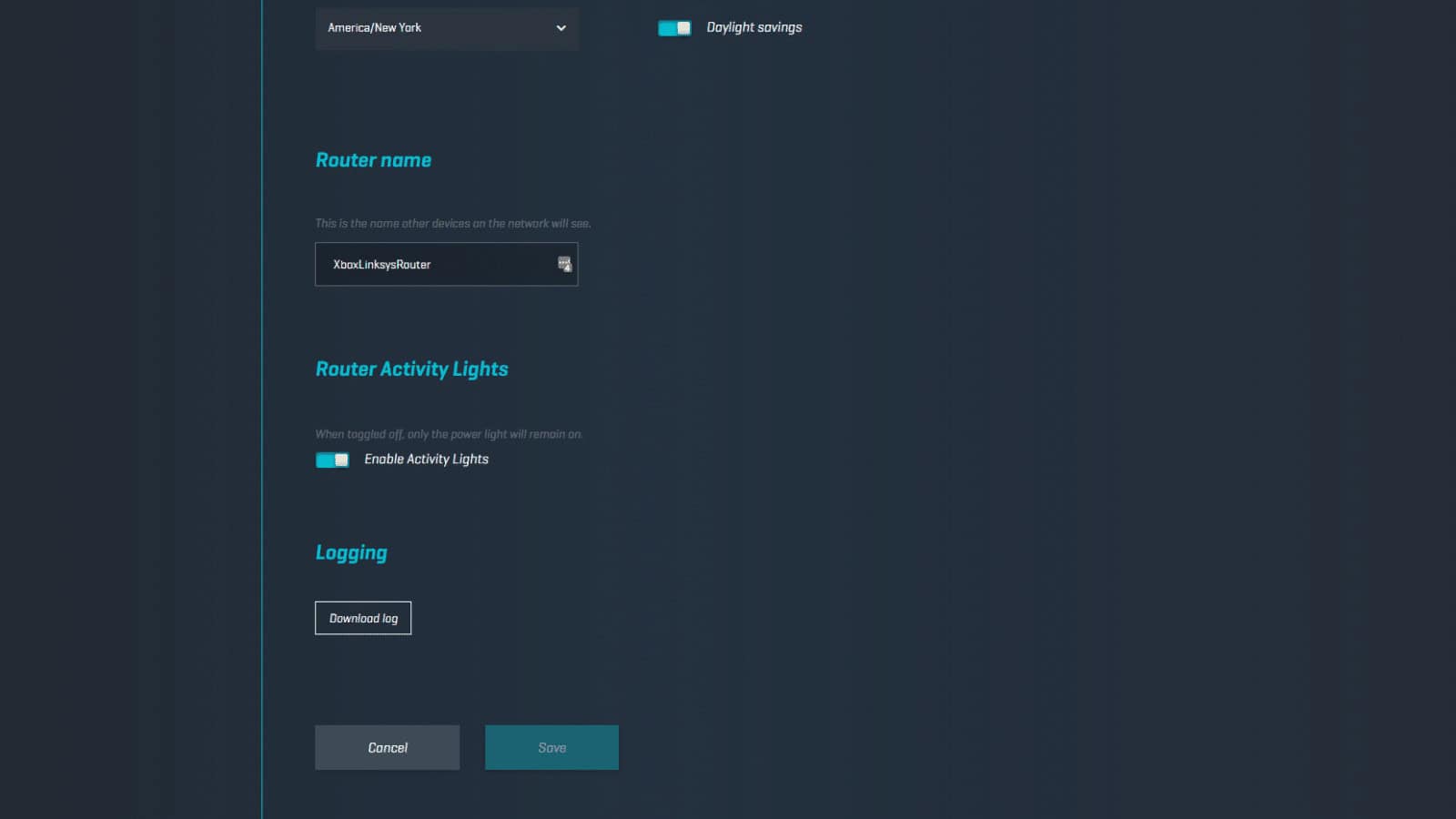 Screenshot: Joe Rice-Jones / KnowTechie
Screenshot: Joe Rice-Jones / KnowTechie
You can also check the page in the Administration section that shows the Media Access Control (MAC) addresses connected to your router. It might also be in the Wireless Configuration, Wireless Status, or DHCP Status List, depending on your router model.
Use this list to count the number of devices attached to your network. Then compare that against your known WiFi devices, if you see 8 devices but you know you only have six – chances are you might have an intruder. It might also be an old gaming console or some other connected device that you don’t use anymore but hasn’t dropped off the router’s list yet.
If you do think someone is actually using your WiFi, there are a few things to do. First, document any MAC addresses connected to the network. Then check with local law enforcement, as the penalties vary greatly nationwide.
If you didn’t already have a WiFi password, put one on now. Make sure it’s WPA2 encryption, that’s the safest and hardest to crack. Also, change your router’s login details, as whoever is on the network might also know those details.
If you already have a WiFi password, look for your pre-shared key in the Wireless or Security settings tabs. Change that, and reboot your router. That will kick off all currently connected devices, so you’ll have to go around all your WiFi devices to give them the new key.
Kick them out in one go
Okay, the easiest way to kick off WiFi leeches is to change the pre-shared key. Once you do that, they’ll all be gone, unless they’re persistent enough to crack your password again, or left malware in your router to allow them to come back to find out the new settings. If you see suspect devices on your WiFi again after changing the key, it’s time to factory reset your router with the 30-30-30 reset.
You can also go one step further, by whitelisting only those MAC addresses belonging to known devices. This will be called MAC filtering, Device filtering, or similar.
What do you think? Are WiFi leeches something you worry about? Let us know down below in the comments or carry the discussion over to our Twitter or Facebook.
Editors’ Recommendations:
- Whoa, Spotify just bumped up free premium trials to 90 days vs its original 30 days
- Anyone living in the U.S with an iPhone can now sign up for the new Apple Card
- Google is launching a new Nest Mini smart speaker with improved sound
- Here’s everything coming to Netflix in September 2019